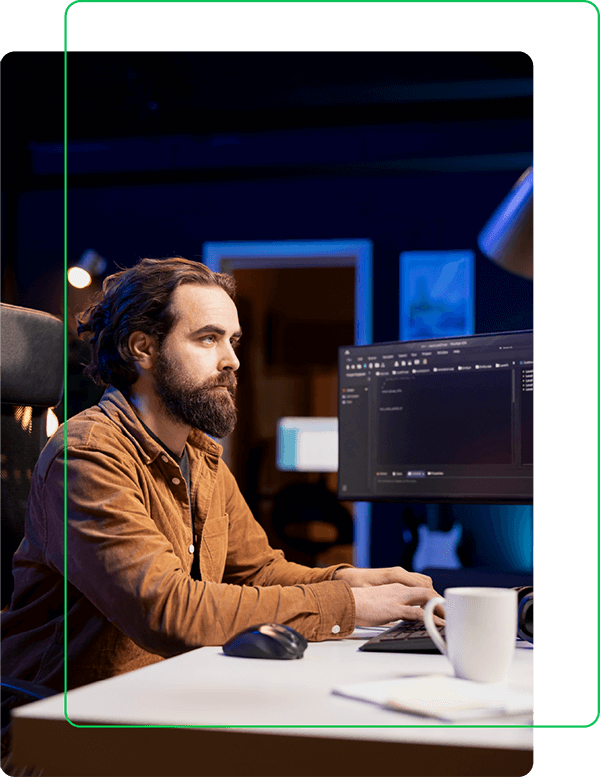
IDENTIFY, TRACK, AND RESPOND TO WIRELESS THREATS INSTANTLY
UNPARALLELED VISIBILITY INTO WIRELESS THREATS
Flying Fox® Enterprise's Real-Time Threat Detection & Forensics provides continuous monitoring, instant alerts, and in-depth forensic analysis of Wi-Fi, Bluetooth, and cellular threats—ensuring organizations can detect, investigate, and neutralize wireless risks before they cause damage.
WHY REAL-TIME THREAT DETECTION MATTERS
WIRELESS THREATS ARE CONSTANTLY EVOLVING—YOUR SECURITY NEEDS TO KEEP UP.

Unauthorized access points, rogue devices, and wireless attacks can go unnoticed without real-time visibility and a forensic trail to track their activity. Flying Fox® Enterprise delivers immediate alerts and deep investigative tools to help security teams rapidly respond to any wireless intrusion.
HOW FLYING FOX REAL-TIME THREAT DETECTION & FORENSICS WORKS

Live Threat Monitoring
Detect rogue Wi-Fi, Bluetooth, and cellular signals in real time.

Instant Alerts & Automated Response
Get notified the moment a security event occurs.

Geo-Locate Wireless Threats
Pinpoint the exact location of rogue devices in secure spaces.

Detailed Forensic Logs & Playback View
Investigate past security events with a full activity timeline.

Correlate Events Across Security Systems
Integrate with SIEM, NAC, and endpoint security tools.

AI/ML-Enhanced Anomaly Detection
Identify suspicious patterns and unknown threats.
EXPLORE MORE SECURITY SOLUTIONS
TSCM (Technical Surveillance Countermeasures)
Neutralizes hidden surveillance devices in classified or secure areas.
IPMS (Integrated Personal Mobility Security)
Protects mobile devicesthrough integrated security protocols.
WIDS (Wireless Intrusion Detection System)
Identifies and blocks rogue Wi-Fi, Bluetooth, and cellular threats.
Wireless Security for Classified Areas
Ensures compliance and prevents unauthorized wireless access.